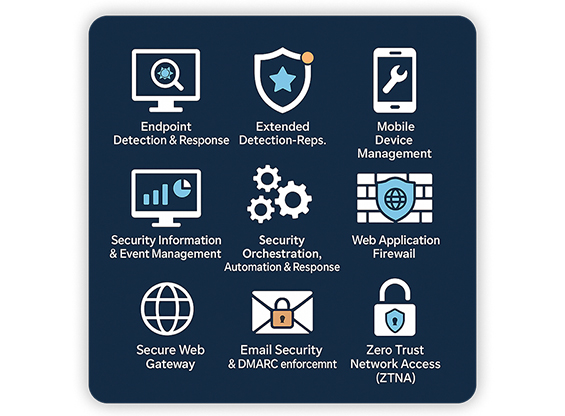
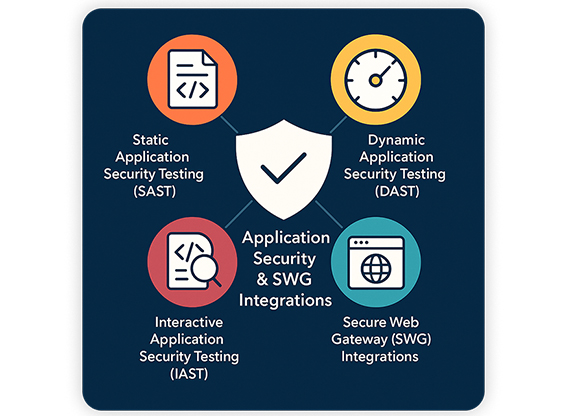
Secure V2 is a core cybersecurity offering under Al Haloul Information Technology Establishment, built by seasoned security and technology professionals with decades of combined experience across enterprise and regulated environments. Our agile, high-performance team brings deep expertise in security architecture, data protection, risk management, compliance, and IT operations.
We operate with a compliance-first mindset—understanding your environment and requirements first, then designing a clear security roadmap aligned with business priorities. From assessment and strategy to implementation and ongoing improvement, we deliver scalable, reliable outcomes with measurable risk reduction and strong ROI.